In today’s threat landscape, cybersecurity is no longer optional—it’s mission critical. From ransomware attacks to zero-day exploits, organizations are under constant pressure to defend their infrastructure.
As a cybersecurity consultant, one truth stands out:
The best professionals are not those who rely on expensive tools—but those who master powerful open-source solutions.
Open-source cybersecurity tools are widely used by ethical hackers, SOC analysts, penetration testers, and blue teams across the globe. They are free, flexible, transparent, and industry-proven.
This guide covers the top 10 must-learn open-source cybersecurity tools that every professional should master in 2026.
Wazuh – SIEM + XDR Platform
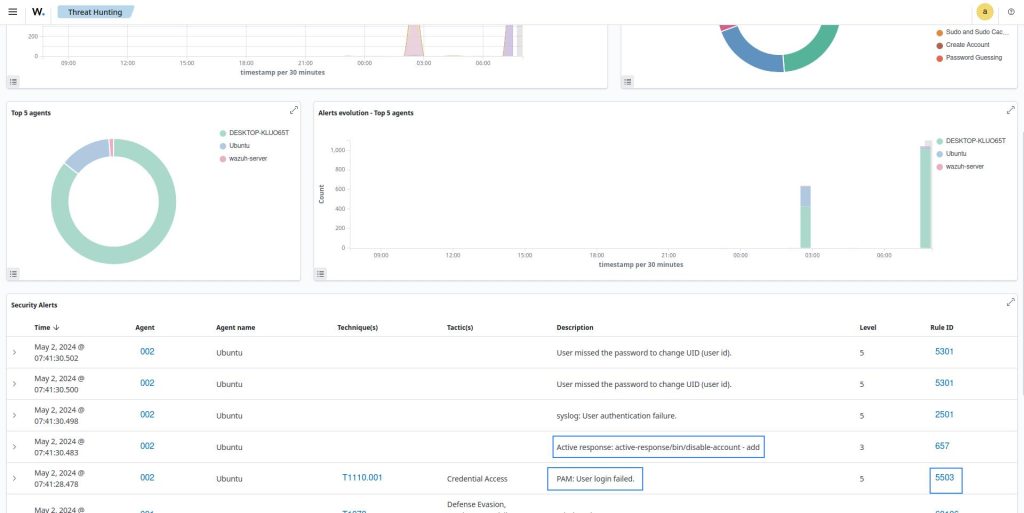
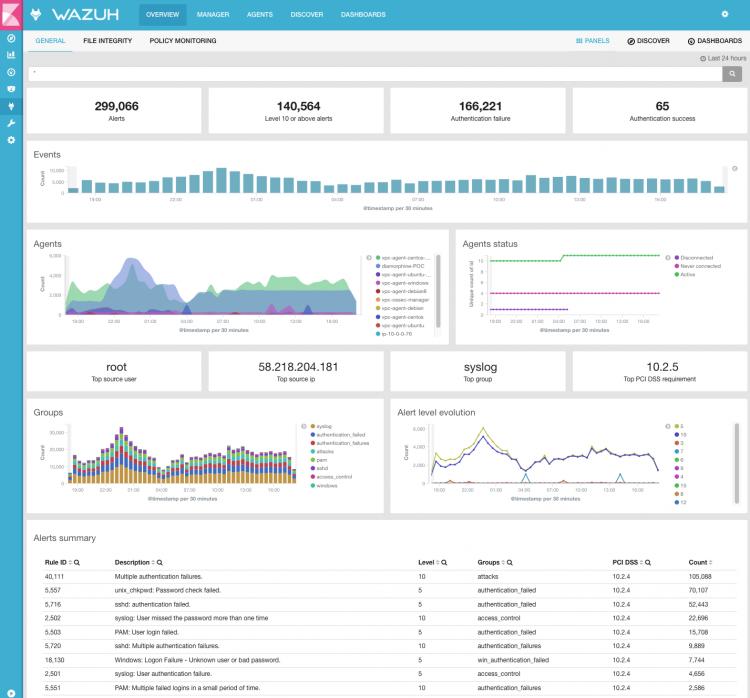
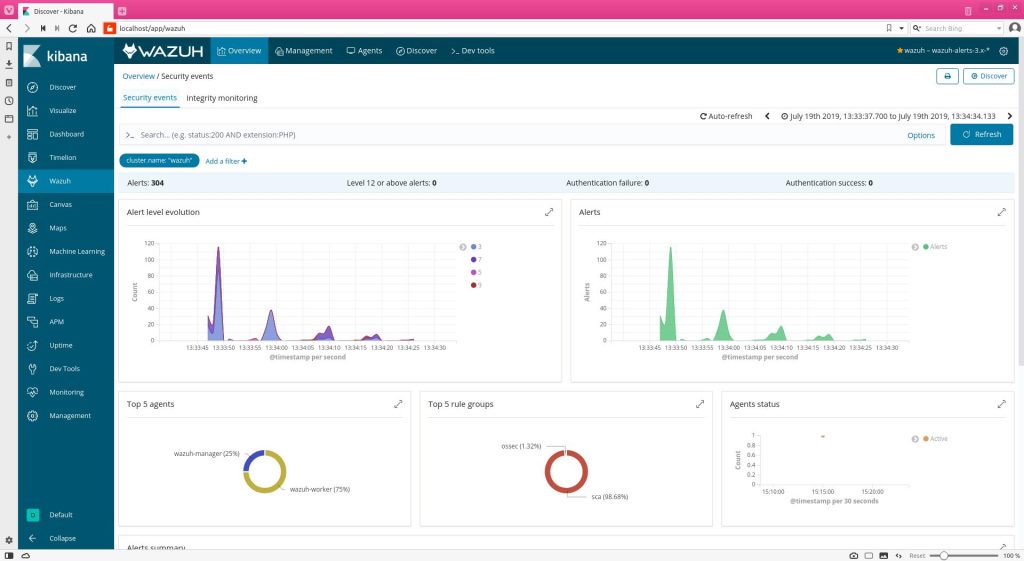
Category: Security Monitoring / SOC
Best For: Blue Teams, SOC Analysts
Wazuh is one of the most powerful open-source platforms combining SIEM (Security Information and Event Management) and XDR (Extended Detection & Response).
It allows you to:
- Monitor endpoints and servers
- Detect threats using rules + AI-based anomaly detection
- Correlate logs across infrastructure
It’s widely used because it delivers enterprise-grade security without licensing costs
👉 If you want to build a SOC (Security Operations Center), this is your starting point.
Nmap – Network Discovery & Scanning
Category: Network Security
Best For: Reconnaissance
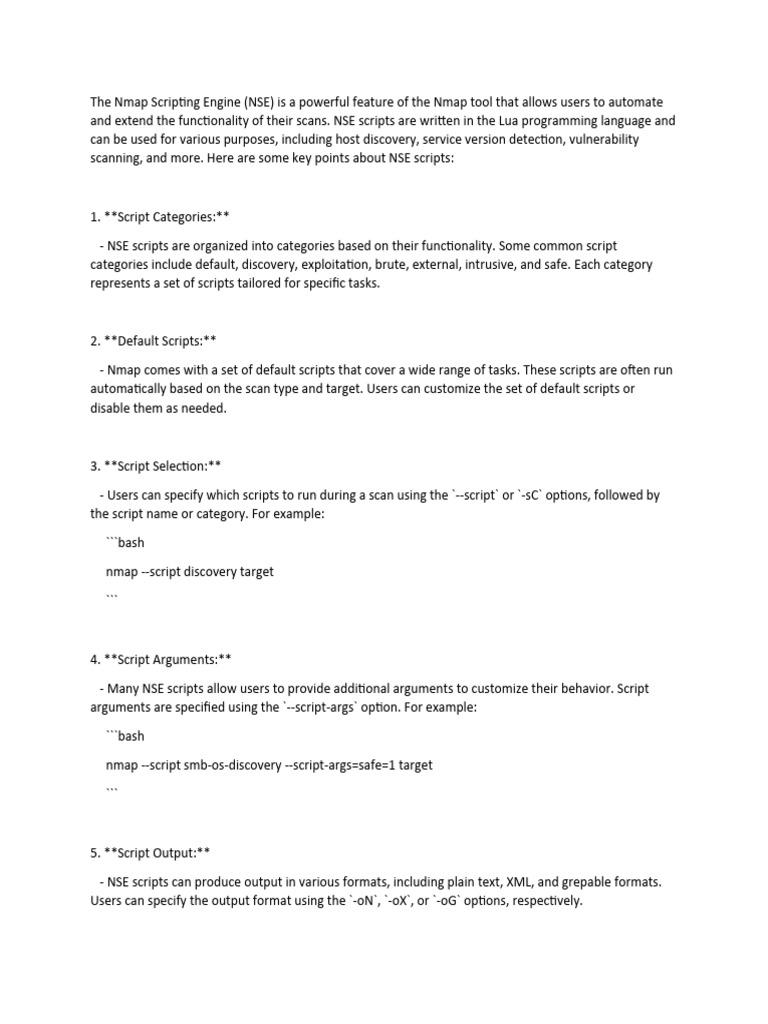
Nmap is a foundational tool for network scanning and reconnaissance.
It helps you:
- Discover live hosts
- Identify open ports
- Detect services and versions
Security professionals use it for:
- Attack surface mapping
- Vulnerability assessment
if you don’t know Nmap, you’re not doing real cybersecurity.
OWASP ZAP – Web Application Security Scanner
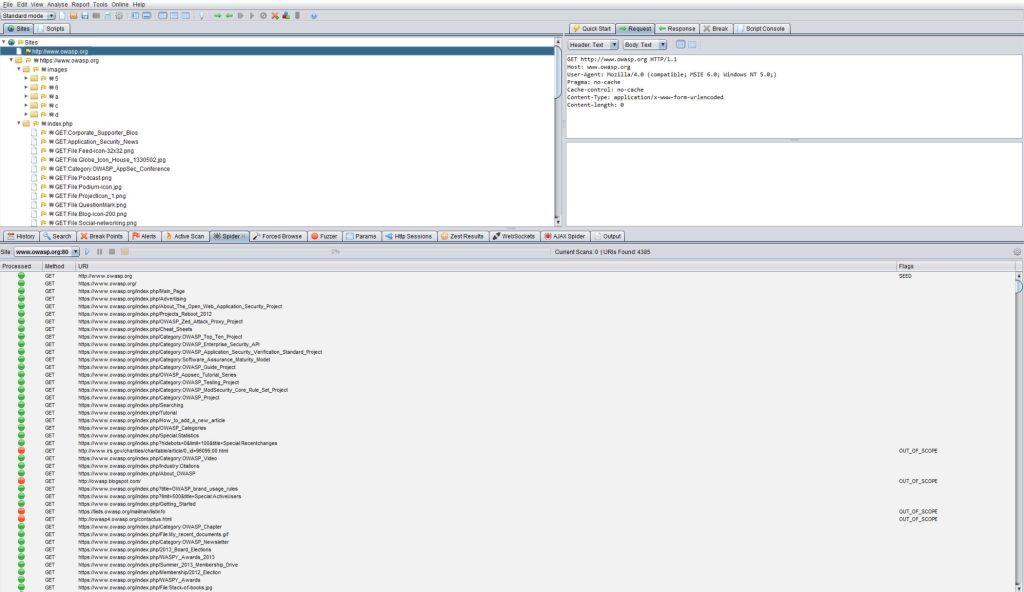
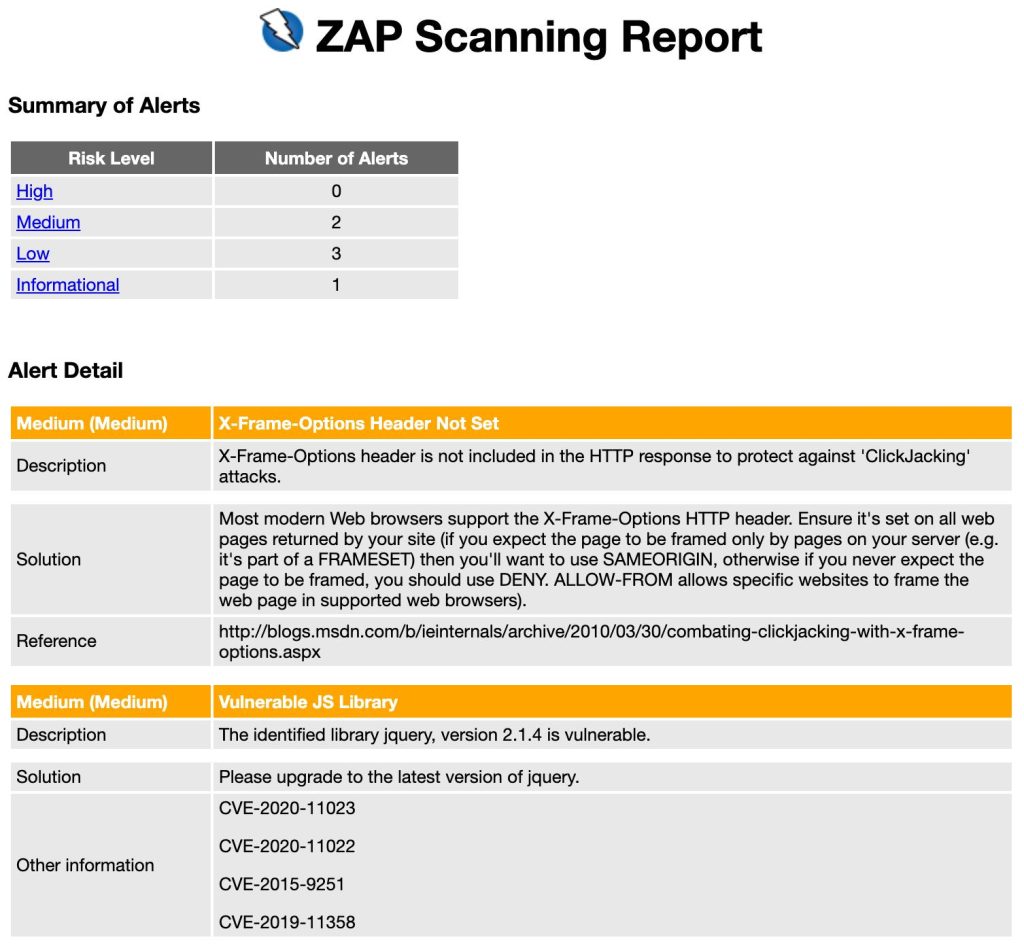
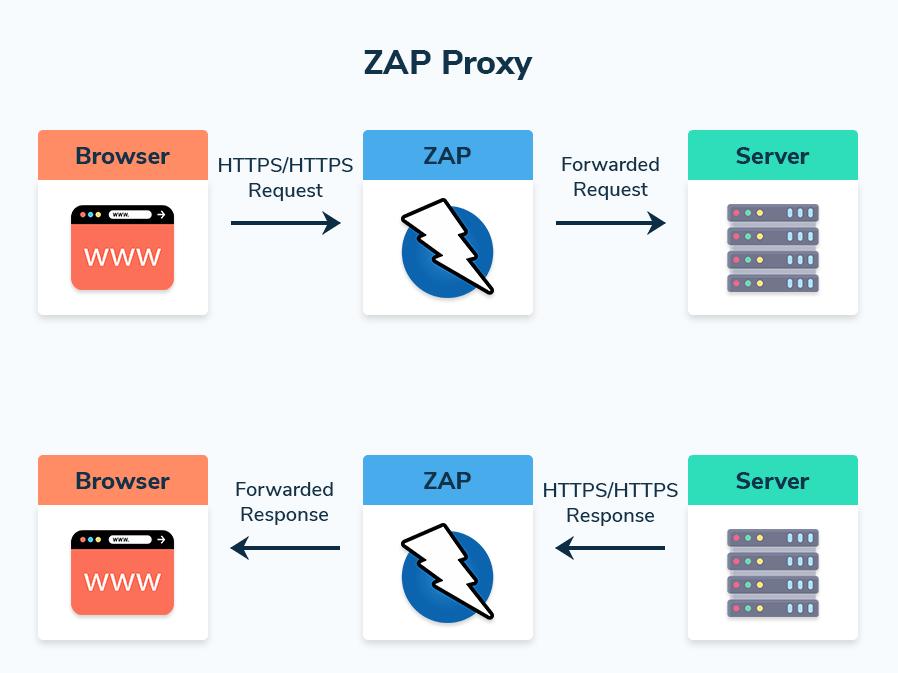
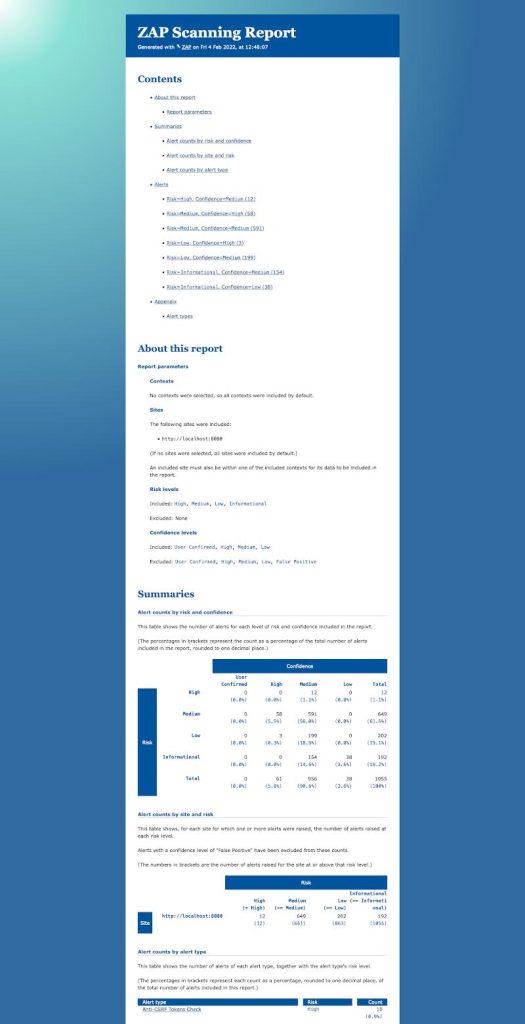
Category: Web Security
Best For: Developers & Pentesters
OWASP ZAP is a widely used tool for identifying web application vulnerabilities.
It detects:
- SQL injection
- XSS (Cross-Site Scripting)
- Authentication flaws
It’s recommended by security communities and developers for testing apps during development
Metasploit Framework – Penetration Testing
Category: Offensive Security
Best For: Ethical Hackers
Metasploit is one of the most powerful tools for:
- Exploit development
- Vulnerability validation
- Post-exploitation
It allows you to simulate real-world attacks and test system defenses.
👉 This is a must-learn tool for penetration testers.
Wireshark – Network Packet Analysis
Category: Network Analysis
Best For: Incident Response
Wireshark captures and analyzes real-time network traffic.
You can:
- Inspect packets
- Detect suspicious traffic
- Analyze malware communication
👉 Essential for forensics and troubleshooting.
OpenVAS – Vulnerability Scanner
Category: Vulnerability Management
Best For: Security Audits
OpenVAS scans systems for:
- Known vulnerabilities
- Misconfigurations
- Security weaknesses
It is widely used in enterprise environments for continuous vulnerability assessment.
Ghidra – Reverse Engineering Framework
Category: Malware Analysis
Best For: Reverse Engineers
Developed by the NSA, Ghidra is used for:
- Malware analysis
- Binary reverse engineering
- Code auditing
It supports multiple architectures and provides deep insights into compiled software
Snort – Intrusion Detection System (IDS)
Category: Network Defense
Best For: Threat Detection
Snort analyzes network traffic in real-time and detects:
- Intrusions
- Malicious activity
- Attack signatures
It is widely used in enterprise networks for defensive security.
Nuclei – Fast Vulnerability Scanner
Category: DevSecOps
Best For: Automation
Nuclei is a modern scanner that uses templates to detect vulnerabilities quickly.
It’s ideal for:
- Bug bounty hunters
- CI/CD security pipelines
It enables automated, scalable vulnerability scanning
TheHive – Incident Response Platform
Category: Incident Response
Best For: SOC Teams
TheHive helps teams:
- Manage security incidents
- Track investigations
- Collaborate across teams
It integrates with SIEM tools like Wazuh to create a complete SOC ecosystem
Final Thoughts (Consultant Perspective)
If you want to succeed in cybersecurity:
Don’t try to learn everything
Master the right tools deeply
Recommended Learning Path:
- Start with Nmap + Wireshark (network basics)
- Move to ZAP + OpenVAS (vulnerability scanning)
- Learn Metasploit + Nuclei (offensive testing)
- Advance to Wazuh + TheHive (SOC operations)
- Finish with Ghidra (advanced analysis)
Closing Insight
Cybersecurity is no longer about tools—it’s about how you think.
But mastering these tools gives you:
- Practical skills
- Industry credibility
- Real-world capability
And the best part?
You can learn all of this for free.



Recent Comments